
Cyber threats are the number one risk to businesses worldwide.
It has remained that way for the past five years.

Your best bet? Find a partner that could ensure the security of your business and its success. What can we do for you?
- Proactive Risk Identification: We find your cyber risks before "they" do.
- Compliance Support: We help you comply with standards and regulations, ensuring you avoid penalties.
- Expert Guidance and Support: We provide you with strategies and help your business navigate the complex cybersecurity landscape, empowering your organization to make informed cybersecurity decisions.
What don't we do?
- We don't try to sell you a broad suite of services. We only provide you with services that are aligned with your real risks.
- We don't offer a one-size-fits-all solution or cookie-cutter reports. Every organization has its unique security needs. Our reports and recommendations are tailored to match your infrastructure.
- We don't claim to do everything. Our expertise lies in identifying and addressing vulnerabilities across your infrastructure, and ensuring your cybersecurity strategy aligns with your business goals.
- We don't follow trends without purpose. We prioritize proven methodologies and focus on delivering effective, high quality services to your organization.
Red Ronin Cybersecurity Services brings you deep technical expertise, and a pragmatic approach to help secure your business and its future. With years of experience in the enterprise and service provider space, we are well-equiped and well-qualified to help you navigate the ever-evolving threat landscape. We are proud to be the first penetration testing and cybersecurity company in the Seychelles, and we are committed to providing the highest quality services to our clients.
Remember, it takes years to build a business, but only a few minutes to destroy it.
Don't let your business become the next statistic. Act today.
Services
Featured Services

Vulnerability Assessment
Identify and address potential security weaknesses with our comprehensive vulnerability assessment. Schedule an assessment to safeguard your business from emerging threats.

Penetration Testing
Uncover and mitigate hidden vulnerabilities with our thorough penetration testing services. Schedule a test to fortify your business against sophisticated cyber threats.

Other Offerings
Receive tailored offerings to effectively secure your business. With our expert consultation, we can assess your business needs and implement strategies to protect your assets.
When should your organization consider conducting a vulnerability assessment?
- Has it been over a year since your last comprehensive vulnerability assessment?
- Have you implemented any significant changes to your IT infrastructure such as network architecture modifications or software installations?
- Is your organization about to engage in compliance audits or certification processes?
- Has your organization recently experienced a security incident or a breach, and looking to prevent similar future occurences?
- Are you about to launch a new customer-facing product or service and would like to ensure your company meets security standards?
If any of your answers were yes, we recommend scheduling a vulnerability assessment.
How will our vulnerability assessments benefit you?
- Cybercriminals are always looking for vulnerabilities to exploit. By identifying and fixing vulnerabilities before they can be exploited, you can reduce your risk of a successful cyberattack.
- A vulnerability assessment helps you prioritize your security efforts. Not all vulnerabilities are created equal. Some are more critical than others. A vulnerability assessment helps you identify the most critical vulnerabilities so you can focus your resources on fixing them.
- Validate your efforts in compliance, risk management by executing a vulnerability assessment today.
What do we offer?
A vulnerability scan of your IT infrastructure will allow us to quickly identify and assess potential vulnerabilities. Unlike a Penetration Test, we will not proceed to exploit the identified vulnerabilities. Therefore, a vulnerability scan is less intrusive and less likely to disrupt your systems.
Our Vulnerability Assessment Packages include:
- Web Applications
- Server/Host Vulnerability Scanning
- Code Review
Deliverables
- i) a comprehensive technical report, detailing our findings and reocmmendations.
- ii) An executive summary, prioritizing the high-risk findings and describing our recommendations.
- iii) A presentation of the high-risk vulnerabilities.
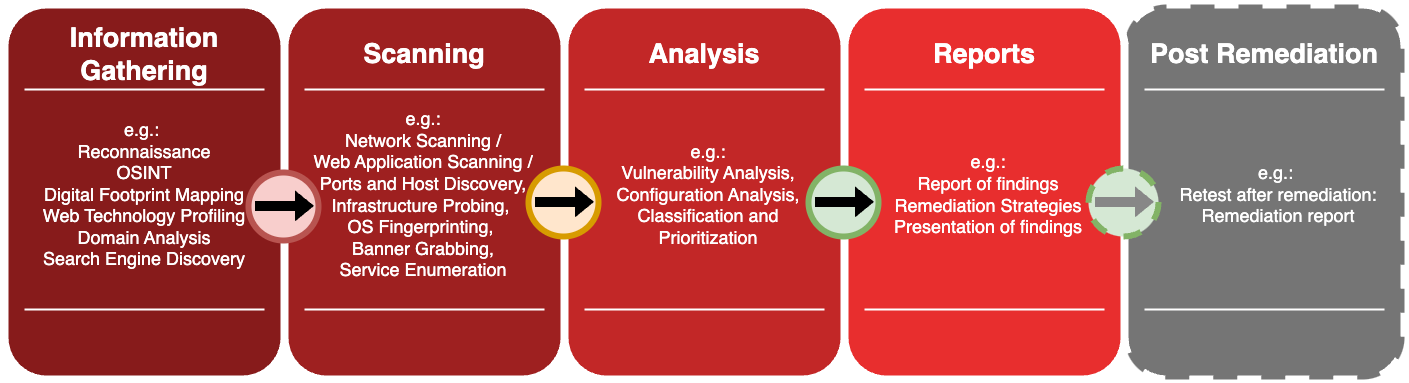
Methodology
Do you really need a Penetration Test?
A Penetration Test goes a step further than a vulnerability assessment. It simulates a real-world attack on your systems in the same way a malicious actor could exploit its vulnerabilities. This activity is typically quite intrusive and can potentially disrupt your systems. Therefore, extreme caution should be taken when considering a Penetration Test. As such, we do not recommend this activity for sensitive critical production systems.
When should you be conducting a Penetration Test? The following are typical scenarios where we recommend it:
- You are about to launch a new high-value application or service.
- You have implemented significant security improvements to address previously identified vulnerabilities, and would like to validate the effectiveness of your remediation efforts.
- You have a regulatory or compliance requirement to conduct a Penetration Test on your systems. Frameworks (PCI DSS, HIPAA, SOC2, ISO 27001) explicitly require regular penetration testing as part of maintaining compliance.
- Your organization is in the process of merging with or acquiring another firm, and you would like to conduct a penetration test as a form of due dilligence.
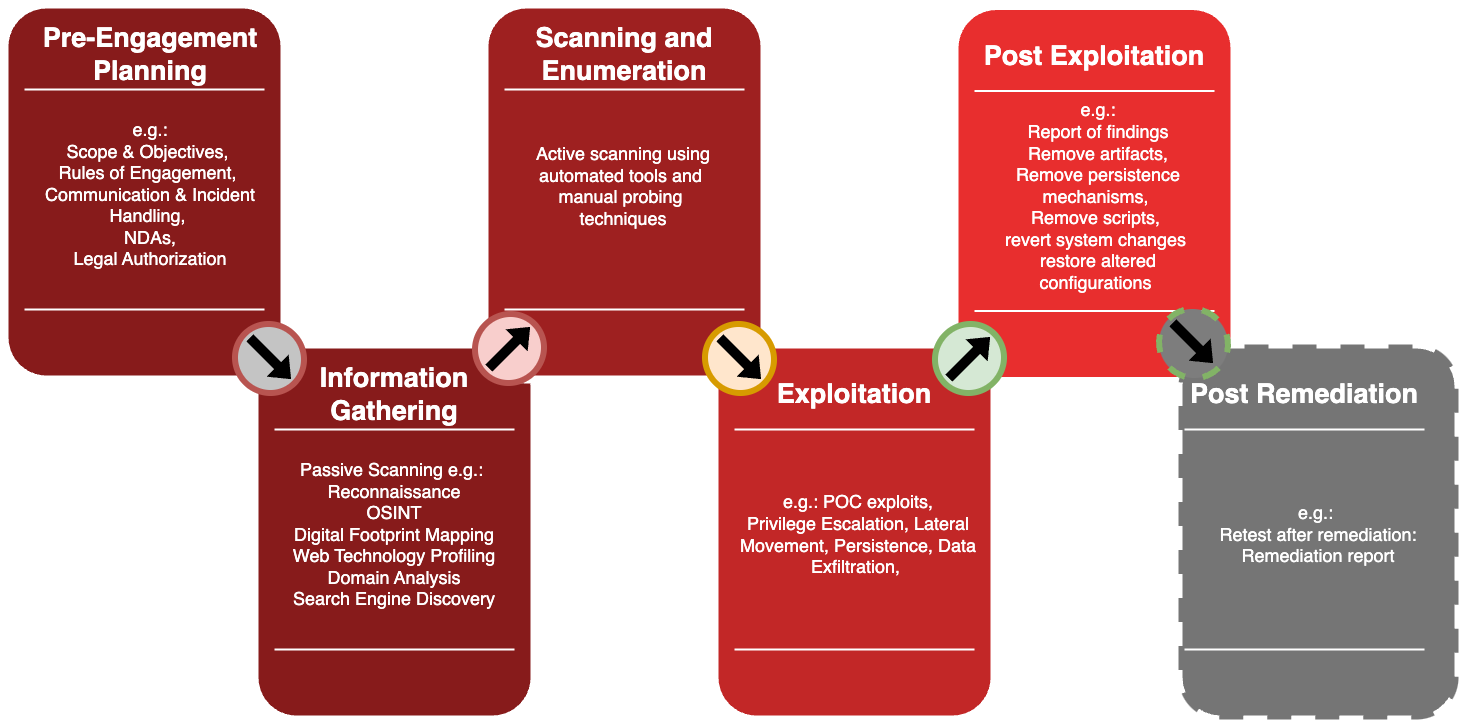
Methodology
Our Penetration Testing methodology adheres to industry-recognized frameworks such as OWASP Top 10 and Penetration Testing Execution Standard (PTES). To quantify and prioritize our findings, we employ the Common Vulnerability Scoring System (CVSS). By using this structured approach, we ensure comprehensive assessment coverage to deliver high quality actionable reports and remediation measures.
What do we offer?
- Blackbox Penetration Tests: A 'blind' test where the tester has no prior knowledge of the target systems. This is useful for simulating an attack from an external threat.
- Whitebox Penetration Tests: A 'full disclosure' test where the tester has full knowledge of the target systems. This is useful for simulating an attack from an internal threat.
- Greybox Penetration Tests: A 'partial disclosure' test where the tester has partial knowledge of the target systems. This is useful for simulating an attack from a threat who has some knowledge of your systems.
Our Penetration Testing Packages include:
- Web Applications
- Server/Host Vulnerability Scanning
- Code Review
Deliverables
- i) a comprehensive technical report with detailed reocmmendations.
- ii) An executive summary, prioritizing the high-risk findings and describing our recommendations.
- iii) A presentation of the high-risk areas
Other Offerings
Whether you are looking for a compliance scan to ensure that your servers are configured with industry best practice, or perhaps wishing to assess the architecture of your network, we can help. Let us know what your needs are, and we will tailor our services to meet your requirements.
Looking for a service that's not listed on our website? Get in touch with us. We are constantly expanding our offerings to better serve our clients.

Team
Credentials
Red Ronin Cybersecurity Services is led by highly skilled individuals with a wealth of experience in the field. Here are some of our credentials:
CISSP
ISC2

PenTest+
CompTIA

Cybersecurity Associate
Cisco Systems Inc.
CCNA
Cisco Systems Inc.

DevNet Associate
Cisco Systems Inc.
eJPT
eLearnSecurity
Contact
Get in touch with us